Malicious AI extensions on VSCode Marketplace steal developer data
[Image blocked: Image]
Fortinet confirms critical FortiCloud auth bypass not fully patched
[Image blocked: Image]
Okta SSO accounts targeted in vishing-based data theft attacks
[Image blocked: Image]
Hackers exploit critical telnetd auth bypass flaw to get root
[Image blocked: Image]
Hackers get $1,047,000 for 76 zero-days at Pwn2Own Automotive 2026
[Image blocked: Image]
ShinyHunters claim to be behind SSO-account data theft attacks
[Image blocked: Image]
Malicious AI extensions on VSCode Marketplace steal developer data
[Image blocked: Image]
CISA confirms active exploitation of four enterprise software bugs
[Image blocked: Image]
US to deport Venezuelans who emptied bank ATMs using malware
[Image blocked: Image]
How to access the Dark Web using the Tor Browser
[Image blocked: Image]
How to enable Kernel-mode Hardware-enforced Stack Protection in Windows 11
[Image blocked: Image]
How to use the Windows Registry Editor
[Image blocked: Image]
How to backup and restore the Windows Registry
[Image blocked: Image]
How to start Windows in Safe Mode
[Image blocked: Image]
How to remove a Trojan, Virus, Worm, or other Malware
[Image blocked: Image]
How to show hidden files in Windows 7
[Image blocked: Image]
How to see hidden files in Windows
[Image blocked: Image]
Qualys BrowserCheck
[Image blocked: Image]
STOPDecrypter
[Image blocked: Image]
AuroraDecrypter
[Image blocked: Image]
FilesLockerDecrypter
[Image blocked: Image]
AdwCleaner
[Image blocked: Image]
ComboFix
[Image blocked: Image]
RKill
[Image blocked: Image]
Junkware Removal Tool
[Image blocked: Image]
eLearning
[Image blocked: Image]
IT Certification Courses
[Image blocked: Image]
Gear + Gadgets
[Image blocked: Image]
Security
[Image blocked: Image]
Best VPNs
[Image blocked: Image]
How to change IP address
[Image blocked: Image]
Access the dark web safely
[Image blocked: Image]
Best VPN for YouTube

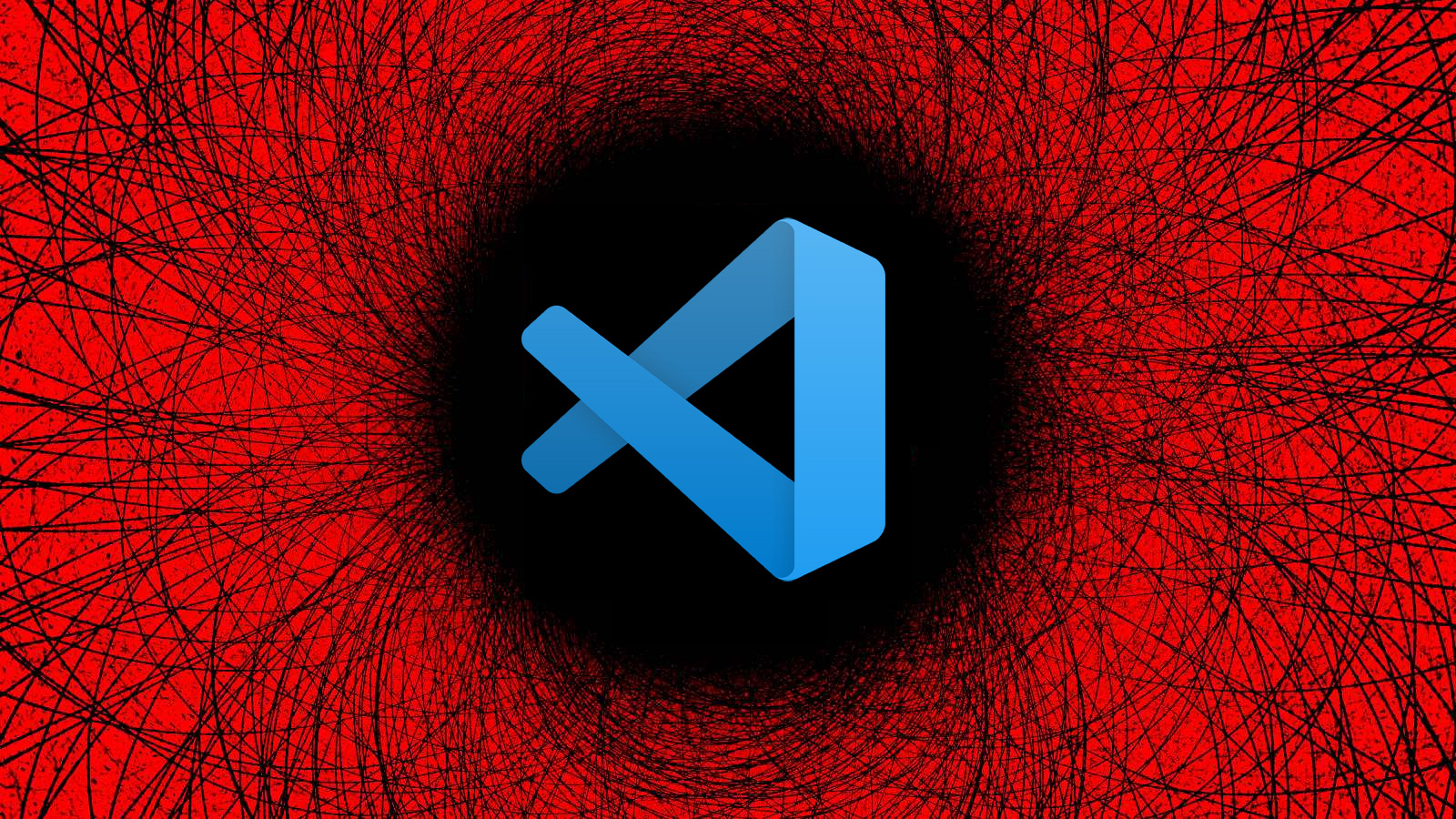
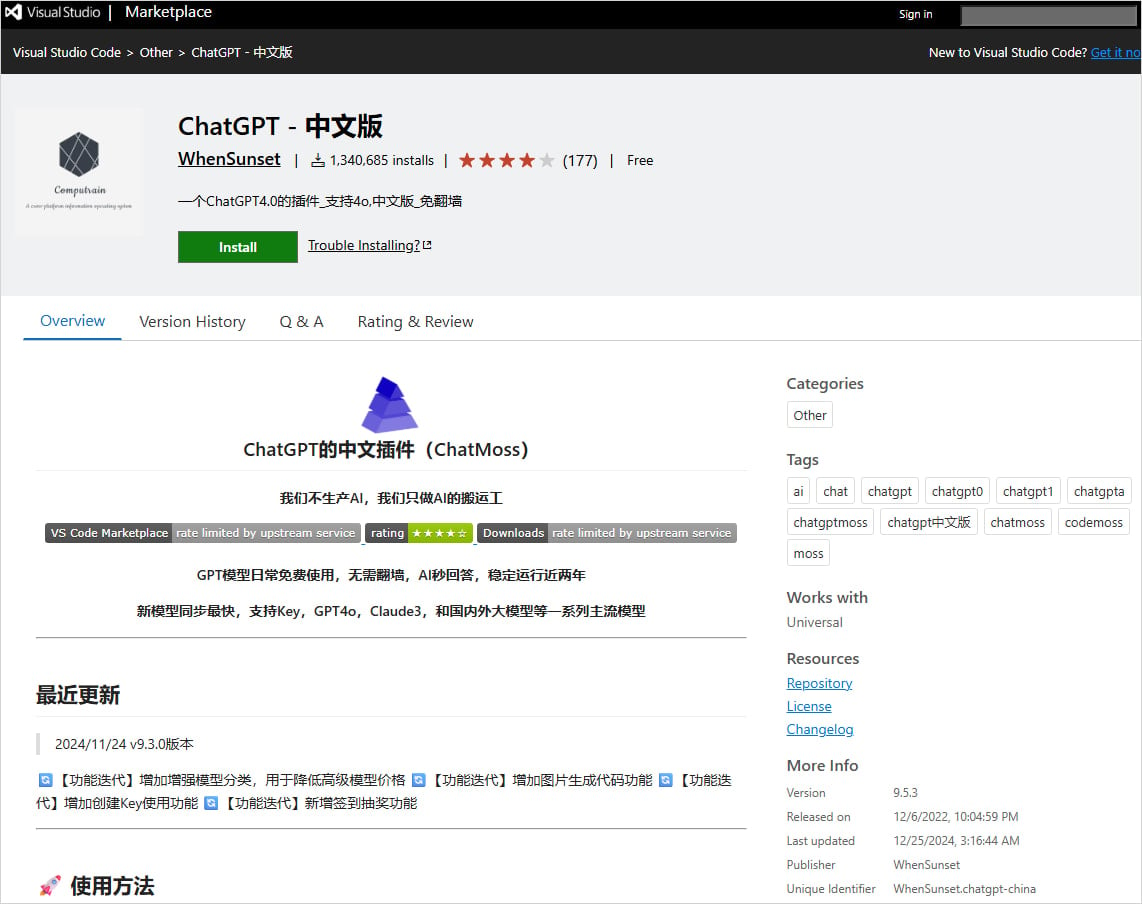
Malicious AI extensions on VSCode Marketplace steal developer data
Two malicious extensions in Microsoft’s Visual Studio Code (VSCode) Marketplace that were collectively installed 1.5 million times exfiltrate developer data to China-based servers.
Both extensions are advertised as AI-based coding assistants that provide the promised functionality. However, they do not disclose the upload activity or ask users for consent to deliver data to a remote server.
The VS Code Marketplace is the official store for add-ons for Microsoft’s popular code editor. VS Code extensions are installable plugins from the marketplace that add features or integrate tools into the editor. One of the most popular add-on categories right now is AI-powered coding assistants.

Researchers at endpoint and supply-chain security company Koi say that the two malicious extensions are part of a campaign they dubbed 'MaliciousCorgi' and share the same code for stealing developer data.
Additionally, both of them use the same spyware infrastructure and communicate with the same backend servers. At publishing time, both are present on the marketplace:
The extensions use three distinct data-collection mechanisms. The first involves real-time monitoring of files opened in the VS Code client. When a file is accessed, its entire contents are encoded in Base64 and transmitted to the attackers’ servers.
Any changes to the opened file are also captured and exfiltrated.
[Image blocked: Image]
"The moment you open any file – not interact with it, just open it – the extension reads its entire contents, encodes it as Base64, and sends it to a webview containing a hidden tracking iframe. Not 20 lines. The entire file," Koi researchers say.
The second mechanism involves a server-controlled file-harvesting command that stealthily transmits up to 50 files from the victim’s workspace each time.
[Image blocked: Image]
The third mechanism uses a zero-pixel iframe in the extension’s webview to load four commercial analytics SDKs: Zhuge.io, GrowingIO, TalkingData, and Baidu Analytics.
These SDKs are used to track user behavior, build identity profiles, fingerprint devices, and monitor activity inside the editor. So, while the first two collect developer work files, the third focuses on user profiling.
Koi Security highlights the risks posed by undocumented functionality in these extensions, including the exposure of private source code, configuration files, cloud service credentials, and .env files containing API keys and credentials.
BleepingComputer has contacted Microsoft about the presence of the two extensions on the VSCode market, but we are still waiting for a reply. We were unable to establish a communication channel with the publisher of the extensions.
[Image blocked: Image]
Secrets Security Cheat Sheet: From Sprawl to Control
Whether you're cleaning up old keys or setting guardrails for AI-generated code, this guide helps your team build securely from the start.
Get the cheat sheet and take the guesswork out of secrets management.
Related Articles:
Microsoft Copilot Studio extension for VS Code now publicly available
VSCode IDE forks expose users to "recommended extension" attacks
Microsoft updates Notepad and Paint with more AI features
Microsoft Copilot is rolling out GPT 5.2 as "Smart Plus" mode
Malicious VSCode Marketplace extensions hid trojan in fake PNG file
Not a member yet? Register Now
You may also like:


[Image blocked: Image]
Fortinet admins report patched FortiGate firewalls getting hacked
[Image blocked: Image]
Hackers breach Fortinet FortiGate devices, steal firewall configs
[Image blocked: Image]
Zendesk ticket systems hijacked in massive global spam wave
[Image blocked: Image]
Identity Governance & Threat Detection in one: Get a guided tour of our platform
[Image blocked: Image]
Overdue a password health-check? Audit your Active Directory for free
[Image blocked: Image]
Exposure Management Index: Insights From 3,000+ Teams. Get The Report.
[Image blocked: Image]
Discover how phishing kits are sold and deployed. Download the full research report.

Terms of Use - Privacy Policy - Ethics Statement - Affiliate Disclosure
Copyright @ 2003 - 2026 Bleeping Computer® LLC - All Rights Reserved

Not a member yet? Register Now
Read our posting guidelinese to learn what content is prohibited.